Filter by
Planar maps, random walks and circle packing
This open access book focuses on the interplay between random walks on planar maps and Koebe’s circle packing theorem. Further topics covered include electric networks, the He–Schramm theorem on infinite circle packings, uniform spanning trees of planar maps, local limits of finite planar maps and the almost sure recurrence of simple random walks on these limits. One of its main goals is t…
- Edition
- 1
- ISBN/ISSN
- 9783030279684
- Collation
- xii; 120 PG; ill.
- Series Title
- -
- Call Number
- 519.282 ASA a
Collaborative technologies and data science in artificial intelligence applic…
In September 2020, researchers from Armenia, Chile, Germany and Japan met at the American University of Armenia for a virtual conference to discuss technologies with applications in smart cities, data science and information theory approaches for intelligent systems, technical challenges for intelligent environments, smart human centered computing, artificial neural networks, and deep learning.…
- Edition
- -
- ISBN/ISSN
- 9783832551414
- Collation
- vii, 190p.; ill.
- Series Title
- -
- Call Number
- 006.3 COL c
Introducing vigilant audiences
This ground-breaking collection of essays examines the scope and consequences of digital vigilantism – a phenomenon emerging on a global scale, which sees digital audiences using social platforms to shape social and political life. Longstanding forms of moral scrutiny and justice seeking are disseminated through our contemporary media landscape, and researchers are increasingly recognising th…
- Edition
- -
- ISBN/ISSN
- 9781783749041
- Collation
- ix, 362 p. ; ill
- Series Title
- -
- Call Number
- 302.231 TRO i
Rational cybersecurity for business : the security leaders' guide to business…
Use the guidance in this comprehensive field guide to gain the support of your top executives for aligning a rational cybersecurity plan with your business. You will learn how to improve working relationships with stakeholders in complex digital businesses, IT, and development environments. You will know how to prioritize your security program, and motivate and retain your team. Misalignment…
- Edition
- -
- ISBN/ISSN
- 9781484259528
- Collation
- xxvi, 333p. : ill.
- Series Title
- -
- Call Number
- 005.8 BLU r
Social media and democracy : the state of the field, prospects for reform
Over the last five years, widespread concern about the effects of social media on democracy has led to an explosion in research from different disciplines and corners of academia. This book is the first of its kind to take stock of this emerging multi-disciplinary field by synthesizing what we know, identifying what we do not know and obstacles to future research, and charting a course for the …
- Edition
- -
- ISBN/ISSN
- 9781108890960
- Collation
- xvii, 345p. : ill.
- Series Title
- -
- Call Number
- 302.231 SOC s
Where truth lies : digital culture and documentary media after 9/11
"This boldly original book traces the evolution of documentary film and photography as they migrated onto digital platforms during the first decades of the twenty-first century. Kris Fallon examines the emergence of several key media forms—social networking and crowdsourcing, video games and virtual environments, big data and data visualization—and demonstrates the formative influence of po…
- Edition
- -
- ISBN/ISSN
- 9780520972117
- Collation
- XVI, 228 p.
- Series Title
- -
- Call Number
- 302.2310973 FAL w
Electronic Iran - the cultural politics of an online evolution
Electronic Iran introduces the concept of the Iranian Internet, a framework that captures interlinked, transnational networks of virtual and offline spaces. Taking her cues from early Internet ethnographies that stress the importance of treating the Internet as both a site and product of cultural production, accounts in media studies that highlight the continuities between old and new media, an…
- Edition
- -
- ISBN/ISSN
- 9780813561943
- Collation
- 168 p.
- Series Title
- -
- Call Number
- 006.754 AKH e
The internet myth: from the internet imaginary to network ideologies
‘The Internet is broken and Paolo Bory knows how we got here. In a powerful book based on original research, Bory carefully documents the myths, imaginaries, and ideologies that shaped the material and cultural history of the Internet. As important as this book is to understand our shattered digital world, it is essential for those who would fix it.’ — Vincent Mosco, author of The Smart C…
- Edition
- -
- ISBN/ISSN
- 9781912656752
- Collation
- xiii, 169p.: ill
- Series Title
- -
- Call Number
- 004.678 BOR i
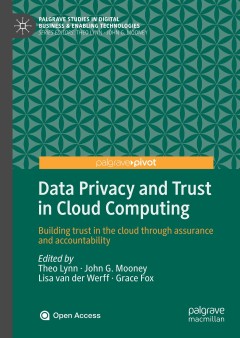
Data privacy and trust in cloud computing : building trust in the cloud throu…
This open access book brings together perspectives from multiple disciplines including psychology, law, IS, and computer science on data privacy and trust in the cloud. Cloud technology has fueled rapid, dramatic technological change, enabling a level of connectivity that has never been seen before in human history. However, this brave new world comes with problems. Several high-profile cases o…
- Edition
- -
- ISBN/ISSN
- 9783030546601
- Collation
- xxi, 149p. : ill.
- Series Title
- -
- Call Number
- 005.8 DAT d

Computer and Information Sciences : 31st International Symposium, ISCIS 2016,…
This book constitutes the refereed proceedings of the 31st International Symposium on Computer and Information Sciences, ISCIS 2016, held in Krakow, Poland, in October 2016. The 29 revised full papers presented were carefully reviewed and selected from 65 submissions. The papers are organized in topical sections on smart algorithms; data classification and processing; stochastic modelling; p…
- Edition
- -
- ISBN/ISSN
- 9783319472171
- Collation
- xiii, 278p. : ill.
- Series Title
- -
- Call Number
- 004 COM c
 Computer Science, Information & General Works
Computer Science, Information & General Works  Philosophy & Psychology
Philosophy & Psychology  Religion
Religion  Social Sciences
Social Sciences  Language
Language  Pure Science
Pure Science  Applied Sciences
Applied Sciences  Art & Recreation
Art & Recreation  Literature
Literature  History & Geography
History & Geography